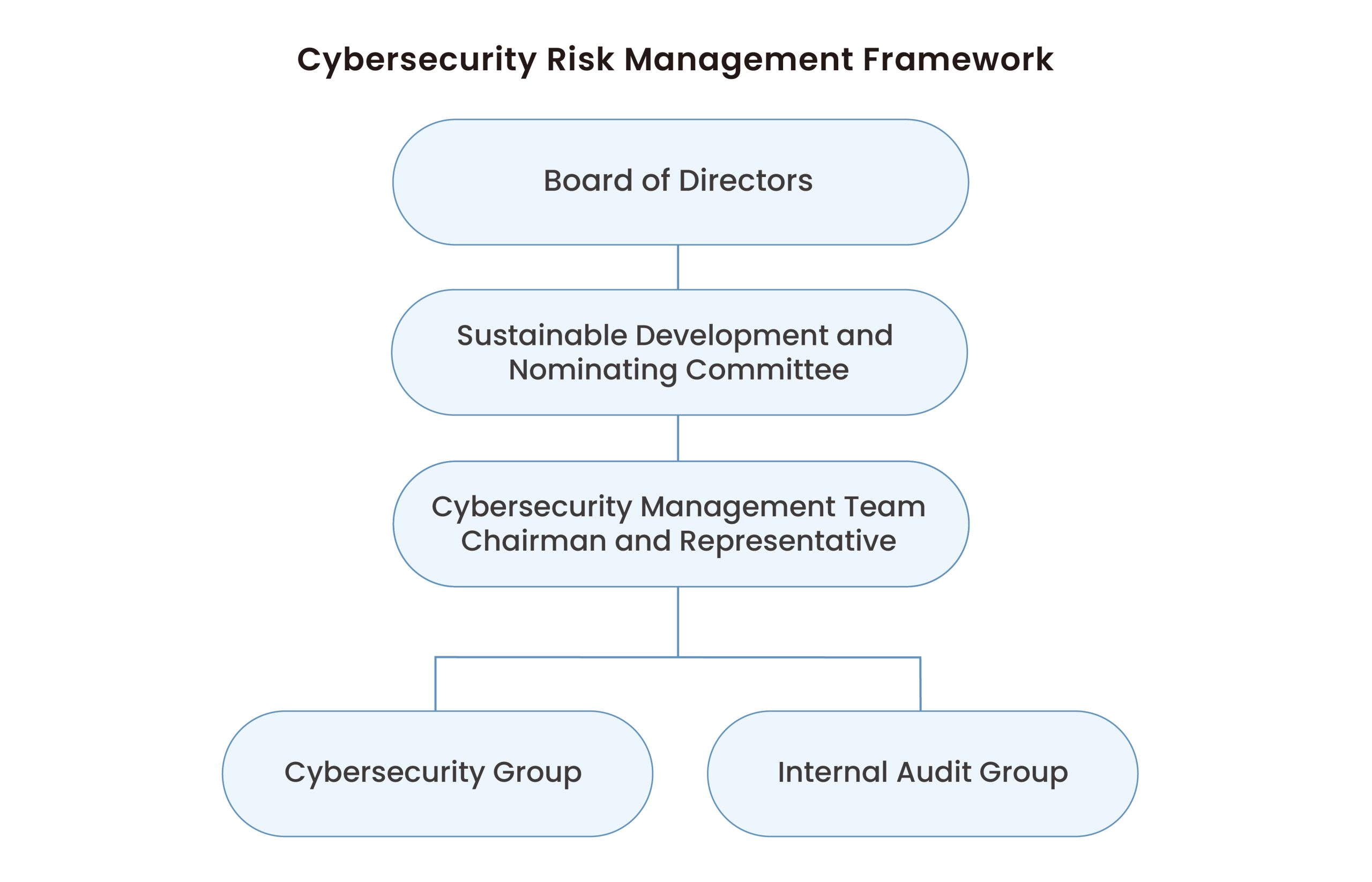
Diamond Biofund has established a Cybersecurity Management Team to formulate and implement cybersecurity policies and execution plans, promoting, reviewing, and improving them. Additionally, the Audit Office forms an Internal Audit Group responsible for conducting cybersecurity audits, performing at least one random check annually to assess the effectiveness of cybersecurity controls and track the results of improvement plans.
Diamond Biofund has established a Cybersecurity Management Team to oversee information and communications security management. The Committee is led by a Management Representative who also serves as the Convener. A Cybersecurity Group and an Internal Audit Group have been set up as the dedicated cybersecurity management units. The implementation status of cybersecurity management is reported annually to the Sustainable Development and Nominating Committee and the Board of Directors. The implementation status for 2024 was reported to the Sustainability Development and Nominating Committee and the Board of Directors on February 25, 2025. The implementation status for 2025 is scheduled to be reported to the Sustainability Development and Nominating Committee and the Board of Directors in the first quarter of 2026.
The Cybersecurity Group includes one dedicated cybersecurity manager and one dedicated cybersecurity staff member, who are responsible for planning, implementing, and controlling tasks related to cybersecurity. Their responsibilities include conducting various risk assessments, system classification, implementing system security control measures, supervising cybersecurity management tasks, and formulating and promoting cybersecurity-related regulations. The Internal Audit Group is responsible for auditing and conducts annual random checks on the implementation of cybersecurity policies, as well as tracking the effectiveness of corrective action plans. A cybersecurity meeting was held in 2025, and no significant cybersecurity violations were reported during the year.
To protect the confidentiality, integrity, and availability of information assets, the company aims to achieve the following goals through the implementation of its cybersecurity policy:
| Cybersecurity Training Course Title | Target Audience (Total Number of People) | Number of Participants | Course Hours | Coverage Rate* |
| ISO27001 Cybersecurity Protection and Personal Data Privacy Training |
All employees (23) | 15 | 3 | 65 |
| AI Applications and Cybersecurity Risk Prevention Course |
All employees (24) | 22 | 3 | 92 |
| Social Engineering and Password Protection Strategies | All employees (23) | 21 | 1.5 | 91 |
*Coverage Rate Calculation = Number of Participants / Total Number of Course Audience
To demonstrate Diamond Biofund’s commitment to cybersecurity and align with international standards, the company initiated the implementation of the ISO 27001 Information Security Management System (ISMS) in the second quarter of 2024. In April 2024, the company established a Cybersecurity Management Committee, which was reorganized in December 2024 into the Cybersecurity Management Team. The Cybersecurity Representative serves as the team convener, and both a Cybersecurity Group and an Internal Audit Group were established as dedicated cybersecurity management bodies. The team reports annually on the execution status of cybersecurity management to the Sustainability and Nomination Committee and the Board of Directors.
Diamond Biofund obtained ISO 27001 certification in September 2024. The certification covers both system and management aspects. The implementation scope includes tasks such as risk assessment, vulnerability remediation, security protection, risk verification, asset inventory and risk evaluation, as well as personnel education and training. All tasks are in compliance with international information security management standards.
Received notification of successful renewal evaluation for the year on September 2, 2025; the certificate remains valid.

| Category | 2025 |
| Number of major cybersecurity incidents | 0 |
| Number of data leaks | 0 |
| Number of employees or customers affected by data leaks | 0 |
| Amount of fines due to cybersecurity incidents (NTD) | 0 |
Note: The definition of major cybersecurity incidents is based on the Financial Supervisory Commission’s FAQ on major announcements for publicly listed companies.
醣基生醫股份有限公司
2017年9月27日登錄興櫃市場交易 (6586:TT)
公司所在地
台北,台灣
公司設立日期
2013
登錄公開市場
2017
公司官網
https://www.chopharma.com/cn/index.html